Roadmap to learn cybersecurity.

1. Essential Skills to Learn
🔹 Networking & System Security
Learn TCP/IP, DNS, VPNs, Firewalls, IDS/IPS, and NAT.
Get familiar with Linux & Windows security.
🔹 Penetration Testing & Ethical Hacking
Learn OWASP Top 10 vulnerabilities.
Practice Web Application Security (SQL Injection, XSS, CSRF).
Work with tools like Burp Suite, Metasploit, Wireshark, and Nmap.
🔹 Programming & Scripting
Python (for automation & security scripting).
Bash or PowerShell (for system administration).
JavaScript (for understanding web security threats).
🔹 Cloud Security & DevSecOps
Learn AWS/Azure security best practices.
Get familiar with CI/CD security and infrastructure as code (IaC).
🔹 Incident Response & Digital Forensics
Learn how to analyze logs and detect cyber threats.
Use tools like Autopsy, Volatility, and ELK Stack (SIEM).
🔹 Governance, Risk, and Compliance (GRC)
Learn ISO 27001, GDPR, PCI-DSS, and NIST standards.
Get familiar with risk assessment frameworks.
2. Certifications to Boost Your Resume
🌟 Entry-Level
✔️ CompTIA Security+
✔️ Cisco CCNA Security
✔️ Certified Ethical Hacker (CEH)
🌟 Intermediate-Level
✔️ Offensive Security Certified Professional (OSCP)
✔️ Certified Information Systems Security Professional (CISSP)
✔️ AWS Certified Security - Specialty
🌟 Advanced-Level
✔️ GIAC Penetration Tester (GPEN)
✔️ Certified Information Security Manager (CISM)
3. Practical Experience to Gain in Nepal
💻 Freelancing & Bug Bounty
Work on Upwork, Fiverr, or Turing as a security consultant.
Participate in bug bounty programs (HackerOne, Bugcrowd).
🔍 Internships & Jobs in Nepal
Apply for cybersecurity roles at banks, fintech companies, IT firms, or government agencies.
Look for security analyst or penetration tester roles in companies like LogPoint, Vianet, eSewa, and Khalti.
🛠️ Open-Source & Personal Projects
Contribute to security-related open-source projects on GitHub.
Set up your own home lab for penetration testing using Kali Linux and Hack The Box.
4. How This Helps You Secure a Job in the UK
✅ Showcases hands-on experience (essential for UK employers).
✅ Proves you have global cybersecurity certifications.
✅ Bug bounty reports can act as real-world proof of expertise.
✅ Open-source contributions make your profile stand out.
What if your background is in software engineering (full-stack development) and you want to transition into cybersecurity, your research should focus on security challenges in software development. Here are some research topics that align with your experience for instance in Node.js, Nest.js, Prisma, PostgreSQL, React, Next.js, and React Native etc……..:
1. Web & API Security
🔹 Securing GraphQL APIs: Common Vulnerabilities and Best Practices
🔹 OWASP Top 10 Security Risks in Modern Web Frameworks: A Study on Next.js and React.js
🔹 API Security in Microservices: A Case Study on Node.js and Nest.js
🔹 Authorization and Authentication Models in Web Applications: A Comparative Study of JWT, OAuth, and Session-Based Authentication
2. Database Security
🔹 SQL Injection and NoSQL Injection Attacks: Security Implications in PostgreSQL and Prisma
🔹 Database Encryption Techniques: Enhancing Security in Prisma ORM
🔹 Role-Based Access Control (RBAC) vs. Attribute-Based Access Control (ABAC): Which is More Secure for Modern Applications?
🔹 Security Threats in Serverless Databases: A Case Study on Neon.tech and PostgreSQL
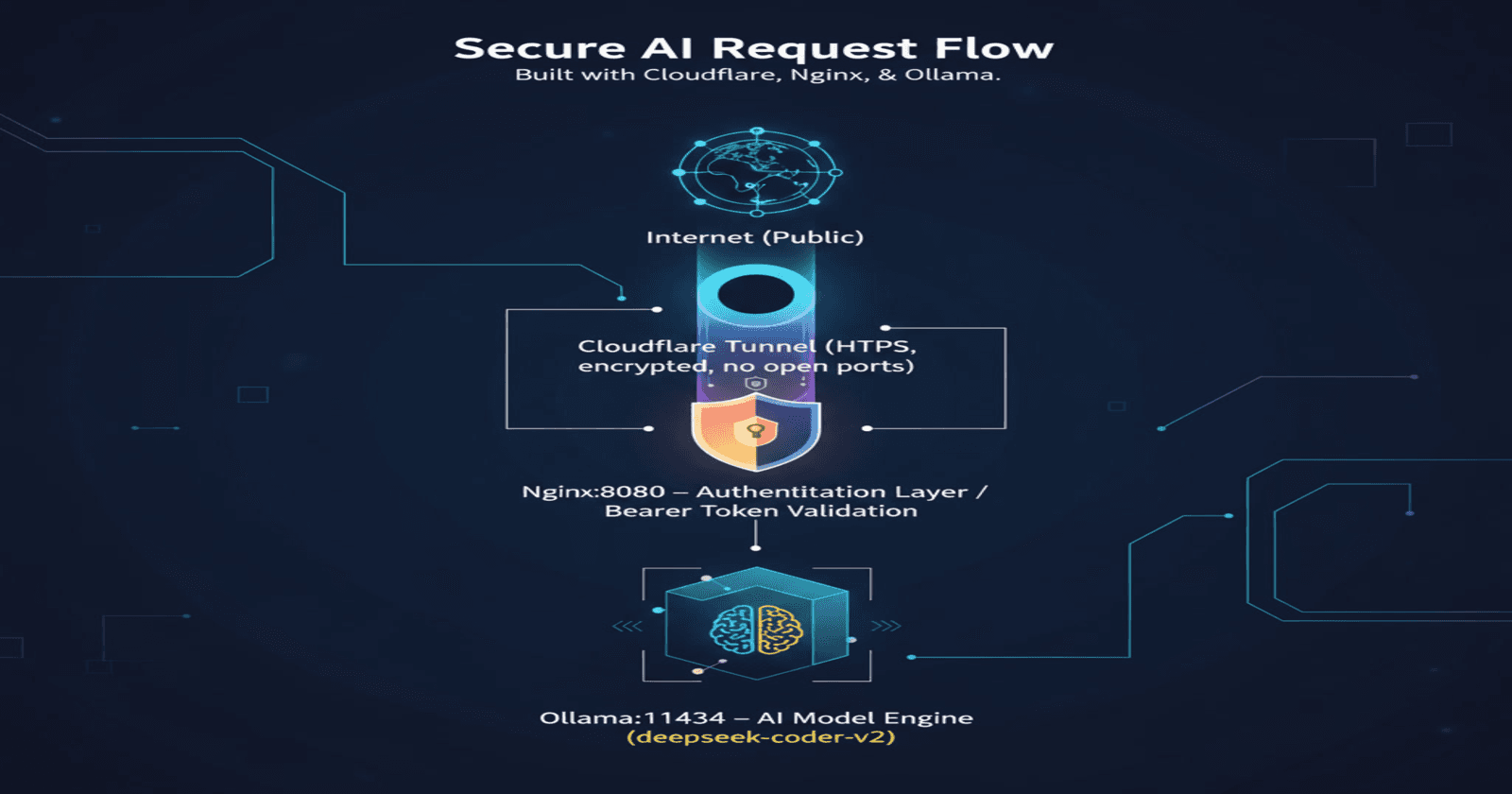
3. Cloud & DevSecOps Security
🔹 CI/CD Pipeline Security: Securing Automated Deployments in Next.js and Node.js
🔹 Cloud-Native Application Security: A Study on Protecting Serverless Functions in AWS and Firebase
🔹 Container Security in DevOps: Protecting Dockerized Applications in Node.js
🔹 Infrastructure as Code (IaC) Security: Best Practices for Terraform and Kubernetes
4. Mobile App Security (React Native)
🔹 Reverse Engineering and Code Obfuscation: Enhancing React Native App Security
🔹 Secure Storage of Sensitive Data in React Native Applications
🔹 Man-in-the-Middle Attacks in Mobile Apps: How Secure is React Native?
🔹 Mobile API Security: Securing Communication Between Frontend and Backend in React Native
5. AI & Cybersecurity
🔹 Using AI for Automated Threat Detection in Web Applications
🔹 Machine Learning for Fraud Detection in Online Transactions
🔹 AI-Driven Security Testing: Enhancing Software Security with GPT-Based Penetration Testing
6. Blockchain & Web3 Security
🔹 Smart Contract Security: Analyzing Vulnerabilities in Solidity-Based Applications
🔹 Blockchain for Identity Management: A Secure Alternative to Traditional Authentication Methods
🔹 Web3 Security: Preventing Phishing and Scams in Decentralized Applications
7. Ethical Hacking & Penetration Testing
🔹 Red Team vs. Blue Team in Web Application Security: A Practical Analysis
🔹 Penetration Testing on Modern JavaScript Frameworks: Case Study on Next.js
🔹 Automating Security Audits for Node.js Applications Using Open-Source Tools